How to Create a Scalable Device Certification System for IoT Devices
A deep dive into architecting reliable certificate provisioning for manufacturing environments
Developer from India.
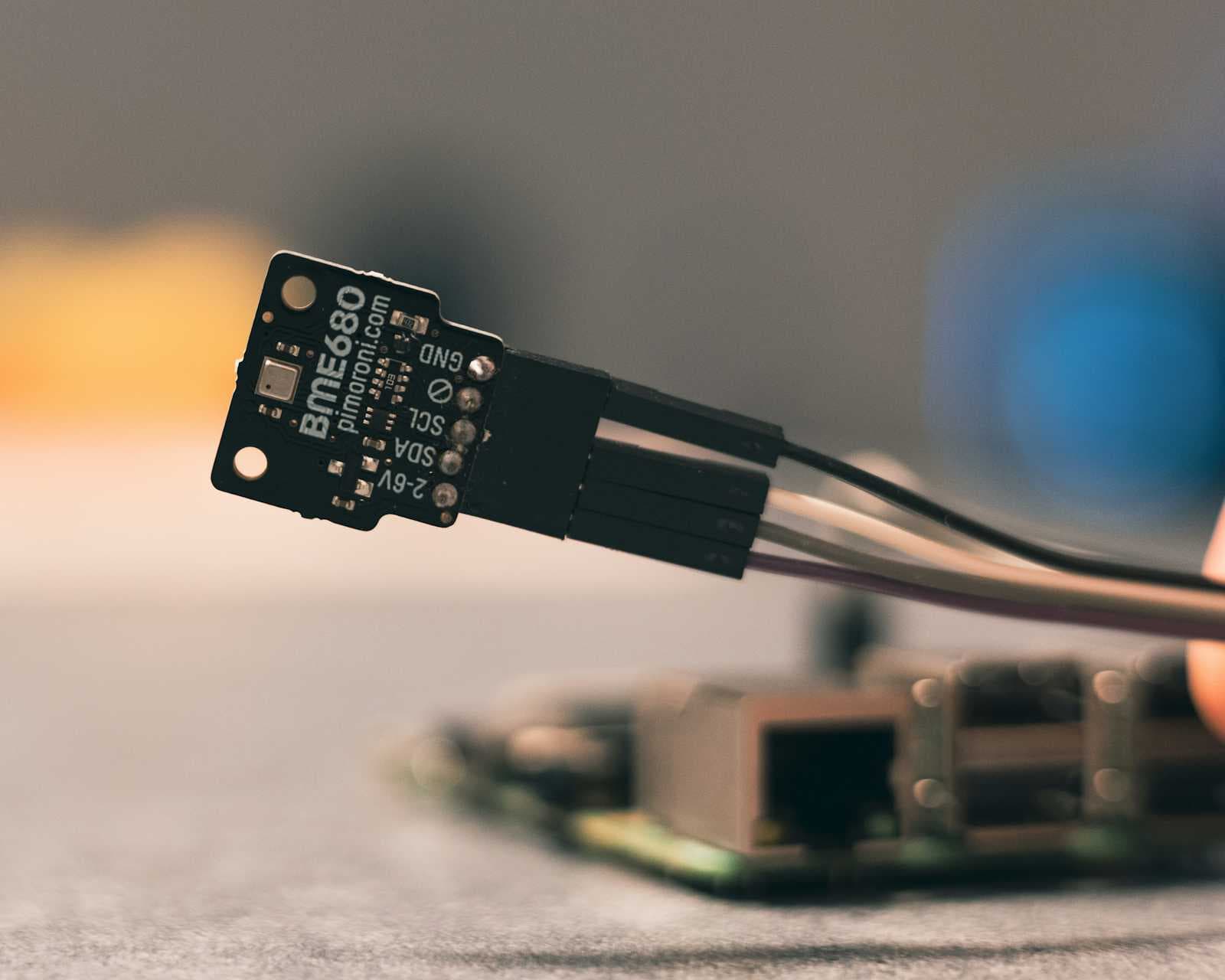
When we set out to build a certification system for IoT devices, the requirements seemed straightforward: issue digital certificates to devices as they roll off production lines. But as we delved deeper, we discovered the fascinating complexity of managing digital identities at manufacturing scale.
Imagine a factory floor where thousands of devices - from simple mobile chips to critical medical equipment like pacemakers - are being produced every hour. Each device needs its unique digital identity, its "birth certificate," before it can securely connect to networks. The stakes? A single failure could mean production lines grinding to a halt, or worse, devices shipping without proper security credentials.
The Core Challenge
Our system needed to act as a reliable broker between two critical worlds: high-speed manufacturing facilities producing thousands of devices per hour, and Certificate Authorities (CAs) like MSCA, EJBCA, AWS, and DigiCertOne that issue digital certificates. Think of it as an air traffic control system for digital identities - ensuring every device gets its credentials from the right provider without any failures. Here's how this looks in practice:
The Communication Dance
When a device first powers on, it needs to establish its identity securely. We implemented this using MQTT with Sparkplug specifications - a lightweight protocol perfect for resource-constrained devices. Each device comes pre-installed with a client during manufacturing:
type DeviceClient struct {
mqttClient mqtt.Client
deviceID string
config SparkplugConfig
status ConnectionStatus
}
func (d *DeviceClient) InitiateProvisioning() error {
topic := fmt.Sprintf("spBv1.0/%s/DBIRTH/%s",
d.config.GroupID, d.deviceID)
message := &SparkplugMessage{
Type: "DBIRTH",
Payload: DeviceInfo{
Manufacturer: d.config.Manufacturer,
Model: d.config.Model,
SerialNum: d.deviceID,
},
}
return d.mqttClient.Publish(topic, message)
}
Security: The Foundation of Trust
In a system managing device identities, security isn't just a feature - it's the core foundation. Every device comes with pre-provisioned security elements:
type DeviceSecurityConfig struct {
initialKey []byte // Initial symmetric key
manufacturerID string // Verified manufacturer identifier
deviceSignature []byte // Hardware-based signature
}
Let's look at how the security components interact:
State Management: The Heart of Reliability
One of the most fascinating challenges we faced was maintaining perfect visibility of each device's provisioning status. We needed to know exactly where each device was in its journey to getting its identity certificate. Here's how we track states:
The state management code ensures no device gets lost in the process:
type ProvisioningStateMachine struct {
deviceID string
currentState DeviceState
stateStore StateStore
eventPublisher EventPublisher
lock *DistributedLock
}
func (sm *ProvisioningStateMachine) TransitionTo(newState DeviceState) error {
if err := sm.lock.Acquire(sm.deviceID); err != nil {
return fmt.Errorf("failed to acquire lock: %w", err)
}
defer sm.lock.Release(sm.deviceID)
// Validate transition
if !sm.isValidTransition(sm.currentState, newState) {
return ErrInvalidStateTransition
}
// Begin transaction
tx := sm.stateStore.BeginTransaction()
defer tx.Rollback()
// Record transition with context
transition := &StateTransition{
FromState: sm.currentState,
ToState: newState,
Timestamp: time.Now(),
Metadata: sm.getTransitionMetadata(),
}
if err := tx.Update(sm.deviceID, transition); err != nil {
return fmt.Errorf("failed to store transition: %w", err)
}
return tx.Commit()
}
Regulatory Compliance and Audit Trails
When you're managing identities for devices that could range from smartphones to medical equipment, maintaining a complete audit trail isn't just good practice - it's often a regulatory requirement:
type AuditRecord struct {
RecordID string
EventType string
Timestamp time.Time
DeviceID string
Actor string
Details struct {
PreviousState DeviceState
NewState DeviceState
Reason string
Location string
CertProvider string
}
ParentRecordID string
HashChain []byte
Signature []byte
}
Each state transition, security event, and certificate operation is recorded with cryptographic proof of integrity. This isn't just about compliance - it's about being able to understand and verify every step in a device's journey to getting its identity.
Real-World Insights
Building and operating this system has taught us several fascinating lessons:
State Management is Everything The complexity isn't in the certificate operations - it's in knowing exactly where each device is in the process and ensuring nothing falls through the cracks.
Security Needs Balance While security is paramount, we needed to balance it with manufacturing speed requirements. The pre-provisioned security elements proved crucial here.
Scale Brings Unexpected Challenges What works perfectly for 100 devices per hour might fail spectacularly at 1000. We learned to build with scale in mind from day one.
Looking Forward
As IoT devices become more prevalent and diverse, the challenges of managing their digital identities will only grow more interesting. We're currently exploring:
Enhanced automation capabilities
More sophisticated monitoring
Advanced device authentication methods
Improved retry strategies
Conclusion
A device certification system might seem straightforward at first glance, but building one that can handle massive scale while maintaining perfect reliability and security is a fascinating challenge. By focusing on state management, security, and audit capabilities, we've created a system that can handle millions of devices while meeting strict regulatory requirements.
Remember: when a device powers on for the first time, it's beginning a journey that will define its entire lifecycle of secure communication. Getting this moment right is crucial for the security of our connected world.